Modern cloud-native applications are built from dozens—sometimes hundreds—of loosely coupled services communicating across networks. While this architectural style improves scalability and deployment flexibility, it also introduces significant complexity in service-to-service communication. Organizations now require a standardized, reliable, and secure way to manage traffic, enforce policies, and observe interactions across distributed systems. This is where service mesh software plays a critical role.
TLDR: A service mesh is a dedicated infrastructure layer that manages service-to-service communication in microservices environments. It improves reliability, security, and observability without requiring changes to application code. Popular tools like Istio, Linkerd, Consul, and Kuma offer different trade-offs in complexity and features. Implementing a service mesh gives organizations granular control over traffic, encryption, and service behavior at scale.
What Is a Service Mesh?
A service mesh is an infrastructure layer that handles communication between services within a distributed application. Instead of embedding communication logic directly into the application code, the mesh moves this responsibility into a dedicated layer.
Most service meshes use a sidecar proxy model. Each application instance is paired with a lightweight proxy that intercepts all inbound and outbound traffic. These proxies communicate with a centralized control plane that manages configuration, policies, and routing rules.

This architecture provides:
- Traffic routing and load balancing
- Mutual TLS (mTLS) encryption
- Observability through metrics, logs, and tracing
- Policy enforcement and access control
- Failure recovery and retries
Why Controlling Service Communication Matters
In traditional monolithic systems, communication occurs within a single process. In microservices architectures, however, every request may cross multiple networks and services before returning a response. Without structured communication management, organizations risk:
- Unreliable service behavior during network failures
- Security vulnerabilities from unencrypted traffic
- Limited visibility into service dependencies
- Difficulty enforcing compliance and policy controls
A service mesh centralizes these concerns and applies consistent policies across the environment. This allows engineering teams to focus on application development instead of rewriting networking logic repeatedly.
Core Capabilities of Service Mesh Software
1. Traffic Management
Service meshes allow fine-grained traffic control. Operators can route requests based on:
- Request headers
- Percentage of traffic
- Geographic region
- Service version
This enables advanced deployment strategies such as:
- Canary releases
- Blue-green deployments
- A/B testing
Traffic policies can be updated dynamically without restarting services.
2. Security and Encryption
Security is one of the most compelling reasons to implement a service mesh. Most modern meshes provide automatic mutual TLS (mTLS) encryption between services.
This ensures:
- Encrypted communication in transit
- Verified service identities
- Reduced lateral movement risk in case of breach
Crucially, encryption happens transparently at the infrastructure layer, requiring no changes to application code.
3. Observability
Modern distributed systems generate vast amounts of communication data. A service mesh collects detailed metrics about:
- Latency
- Error rates
- Request volume
- Dependency mapping

This unified visibility allows teams to quickly identify bottlenecks and trace failures across service boundaries.
4. Resilience and Fault Tolerance
Built-in resiliency features include:
- Retries
- Timeouts
- Circuit breakers
- Failover handling
Instead of writing custom retry logic into each service, organizations configure these behaviors centrally. This reduces code duplication and improves reliability.
Leading Service Mesh Solutions
Several mature service mesh platforms dominate the cloud-native ecosystem. Each offers distinct strengths and operational considerations.
1. Istio
Istio is one of the most widely adopted service meshes. Built to run on Kubernetes, it provides extensive traffic control, security policies, and observability features.
Strengths:
- Rich feature set
- Strong community support
- Advanced traffic management capabilities
Challenges:
- Operational complexity
- Steeper learning curve
2. Linkerd
Linkerd focuses on simplicity, performance, and ease of adoption. It emphasizes minimal configuration while still offering strong security defaults.
Strengths:
- Lightweight architecture
- Simpler installation and management
- Strong default security posture
Challenges:
- Fewer advanced configuration features compared to Istio
3. Consul Service Mesh
HashiCorp Consul integrates service discovery and service mesh capabilities. It works across Kubernetes and non-Kubernetes environments.
Strengths:
- Multi-platform support
- Strong integration with HashiCorp ecosystem
- Flexible deployment options
Challenges:
- More configuration needed in complex setups
4. Kuma
Kuma, built by Kong, is designed for simplicity and multi-zone deployments. It supports both Kubernetes and virtual machine environments.
Strengths:
- User-friendly design
- Multi-cluster support
- Based on Envoy proxy
Challenges:
- Smaller community compared to Istio
Comparison Chart of Popular Service Mesh Tools
| Feature | Istio | Linkerd | Consul | Kuma |
|---|---|---|---|---|
| Primary Environment | Kubernetes | Kubernetes | Kubernetes and VM | Kubernetes and VM |
| Ease of Setup | Moderate to Complex | Simple | Moderate | Simple to Moderate |
| Traffic Management Depth | Advanced | Moderate | Moderate | Moderate |
| mTLS Support | Yes | Yes | Yes | Yes |
| Multi-Cluster Support | Yes | Limited | Yes | Yes |
| Best For | Enterprise-scale environments | Simplified Kubernetes deployments | Hybrid infrastructure | Flexible multi-zone setups |
Architecture Overview
A typical service mesh consists of two main components:
- Data Plane: The sidecar proxies that intercept traffic.
- Control Plane: The centralized management component that configures proxies.
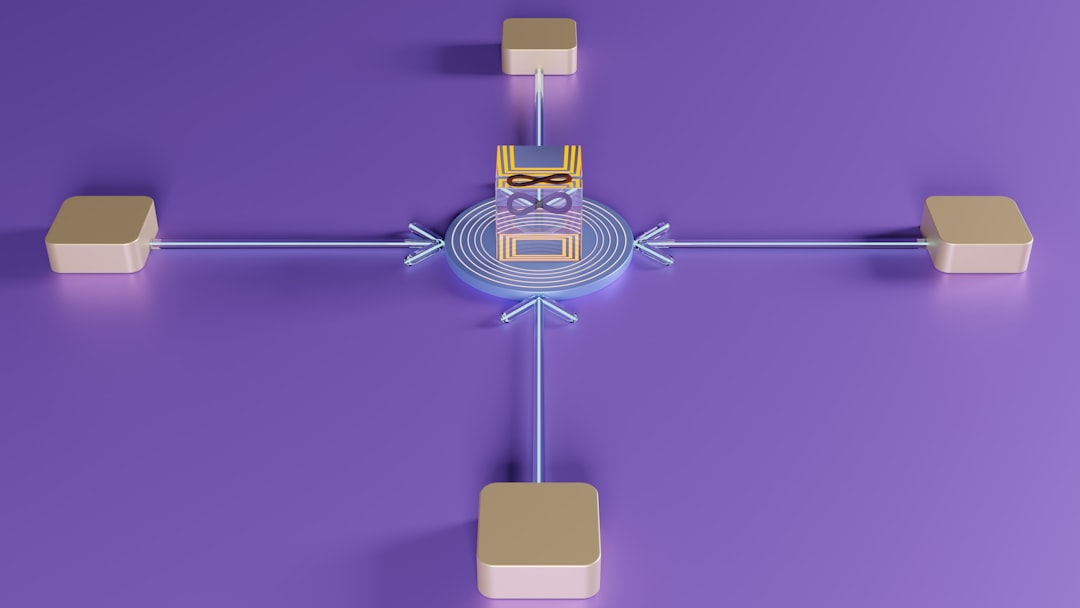
The control plane distributes configuration policies to proxies in real time. The proxies then enforce routing rules, security policies, and telemetry collection autonomously.
Operational Considerations
While service meshes offer substantial benefits, they introduce added operational layers. Organizations must consider:
- Resource overhead: Sidecars consume CPU and memory.
- Operational complexity: Teams require mesh-specific expertise.
- Monitoring requirements: Observability must integrate into existing monitoring stacks.
Careful planning and phased deployment are essential. Many organizations begin by enabling observability features before moving to full mTLS enforcement.
When Should You Implement a Service Mesh?
A service mesh is most beneficial when:
- You operate large-scale microservices architectures
- You require strict security compliance and encryption
- You manage frequent deployments across multiple teams
- You need advanced traffic routing capabilities
For smaller or simpler systems, the operational complexity may outweigh the benefits. However, for mature cloud-native environments, a service mesh provides essential governance and reliability controls.
The Strategic Value of Service Mesh Technology
As organizations scale distributed systems, the challenge shifts from building services to managing their interactions. Communication patterns become as important as application logic. Service mesh software provides a disciplined, centralized, and secure method for controlling these interactions.
By separating communication concerns from application code, enterprises gain:
- Improved deployment agility
- Strengthened security posture
- Enhanced operational visibility
- Reduced developer burden
In an era where system complexity continues to grow, service mesh technology serves as a foundational control layer. It transforms chaotic service-to-service traffic into governed, observable, and secure interactions—allowing organizations to innovate with confidence while maintaining reliability and compliance.
For companies committed to cloud-native principles, adopting a service mesh is no longer experimental; it is increasingly a strategic necessity.