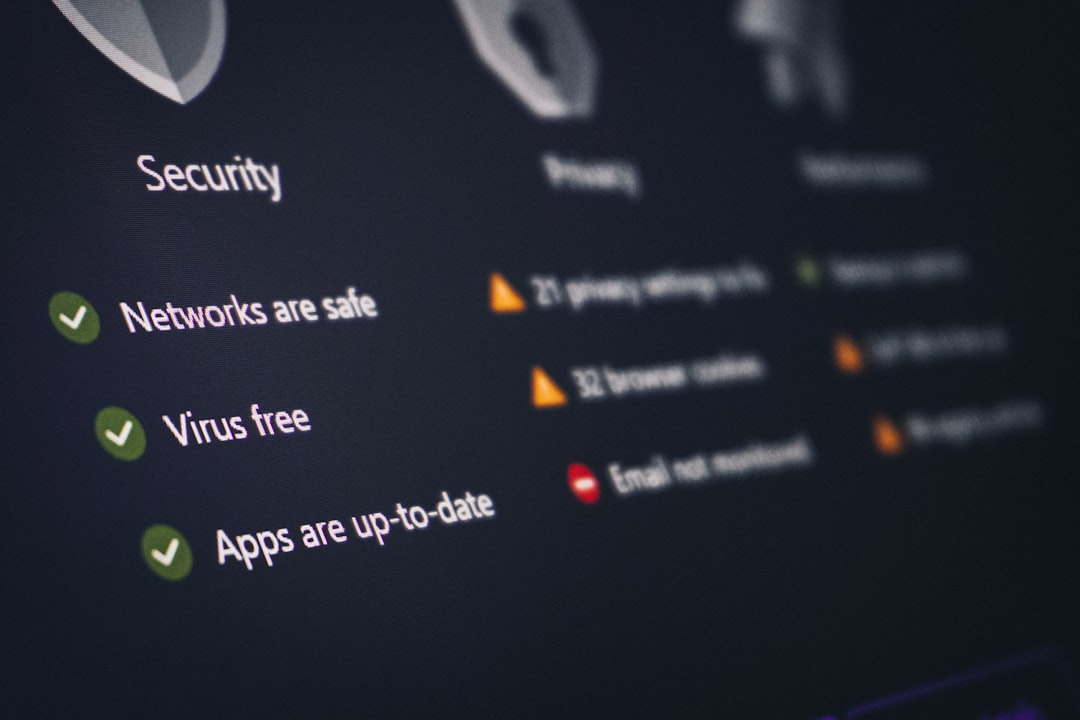
Modern websites face an unprecedented range of cyber threats, from automated bot attacks to highly targeted data breaches. As businesses increasingly rely on digital platforms to serve customers, process payments, and store sensitive information, the importance of robust website security tools cannot be overstated. A single vulnerability can lead to financial loss, reputational damage, regulatory penalties, and loss of customer trust. Building a secure website environment requires a layered, strategic approach supported by reliable and continuously updated security tools.
TL;DR: Website security tools are essential for protecting against malware, data breaches, DDoS attacks, and other evolving cyber threats. Effective protection requires a layered approach that includes firewalls, malware scanners, SSL encryption, monitoring systems, and regular updates. No single tool can provide complete security; instead, organizations should combine multiple solutions for comprehensive defense. Proactive monitoring and continuous improvement are critical to staying ahead of attackers.
Cyber threats evolve constantly. Attackers leverage automation, artificial intelligence, and vast botnets to identify and exploit weaknesses within seconds. Organizations that fail to implement comprehensive security measures risk becoming easy targets. Fortunately, a wide range of website security tools exist to help identify vulnerabilities, block malicious traffic, and safeguard sensitive data.
1. Web Application Firewalls (WAF)
A Web Application Firewall (WAF) is one of the most critical defenses for any website. A WAF filters and monitors HTTP traffic between a web application and the internet. It acts as a protective barrier, detecting and blocking malicious requests before they reach the web server.

WAF tools are particularly effective against:
- SQL injection attacks
- Cross-site scripting (XSS)
- Cross-site request forgery (CSRF)
- File inclusion attacks
- Zero-day exploits
Modern WAFs use both signature-based detection and behavioral analysis. This dual capability allows them to block known threats while also identifying suspicious patterns that may indicate emerging attack techniques. For businesses handling customer credentials or payment information, deploying a WAF is not optional—it is foundational.
2. SSL/TLS Certificates and Encryption Tools
Encryption is the backbone of secure communication on the internet. SSL (Secure Sockets Layer) and its successor TLS (Transport Layer Security) encrypt data transmitted between users and servers, preventing interception by unauthorized parties.
When properly implemented, encryption tools:
- Protect login credentials and personal data
- Secure payment transactions
- Enhance customer trust with HTTPS indicators
- Improve search engine rankings
Beyond basic SSL certificates, organizations should implement strong cipher suites, enable HTTP Strict Transport Security (HSTS), and regularly renew certificates to avoid service interruptions. Encryption alone does not stop attacks, but it significantly reduces the risk of data exposure.
3. Malware Scanners and Removal Tools
Malware infections can occur through vulnerable plugins, outdated software, compromised credentials, or insecure hosting environments. Once inside a system, malware can redirect users, steal information, or inject malicious scripts.
Automated malware scanning tools continuously monitor website files, databases, and configurations to detect:
- Hidden backdoors
- Unauthorized file changes
- Malicious scripts
- SEO spam injections
- Suspicious redirects
Effective tools offer real-time alerts, quarantine capabilities, and one-click remediation. However, automated removal should always be supplemented with manual review to ensure no trace of the infection remains. Regular scanning schedules are crucial, as attackers often reinfect vulnerable sites.
4. Intrusion Detection and Prevention Systems (IDS/IPS)
Intrusion Detection Systems (IDS) monitor network traffic for suspicious activity, while Intrusion Prevention Systems (IPS) actively block identified threats. These systems analyze traffic patterns and flag anomalies that might indicate brute force attempts, privilege escalation, or reconnaissance scanning.
IDS and IPS solutions are valuable because they provide:
- Real-time traffic monitoring
- Detailed logging for forensic analysis
- Automated blocking of high-risk IP addresses
- Threat intelligence integration
For organizations with complex infrastructures or high traffic volumes, implementing IDS/IPS systems can significantly reduce response time to potential breaches. Early detection often determines whether an incident becomes a minor disruption or a major crisis.
5. DDoS Protection Services
Distributed Denial-of-Service (DDoS) attacks attempt to overwhelm websites with massive amounts of traffic, causing service outages. These attacks can disrupt operations, damage brand reputation, and result in substantial revenue loss.
DDoS protection tools operate by:
- Identifying abnormal traffic surges
- Filtering malicious requests
- Distributing traffic across multiple servers
- Leveraging content delivery networks (CDNs)
Advanced DDoS mitigation platforms use machine learning algorithms to distinguish legitimate users from bots. The ability to absorb and filter large-scale attacks ensures that websites remain accessible even during peak threat activity.
6. Security Information and Event Management (SIEM)
SIEM solutions centralize security data from multiple sources, including servers, firewalls, applications, and endpoint devices. They aggregate logs, correlate events, and generate alerts based on suspicious patterns.
Key benefits of SIEM tools include:
- Comprehensive visibility across systems
- Regulatory compliance reporting
- Automated incident response workflows
- Advanced threat correlation
By consolidating security data into a single interface, SIEM platforms enable security teams to identify coordinated attacks that might otherwise go unnoticed. In complex enterprise environments, SIEM functionality is indispensable.
7. Vulnerability Scanning and Penetration Testing Tools
Proactive vulnerability management is a cornerstone of website security. Vulnerability scanners automatically identify outdated software, misconfigurations, and known security gaps within web environments.
Common scanning targets include:
- Outdated CMS versions
- Unpatched plugins and extensions
- Open ports and exposed services
- Weak authentication mechanisms
Penetration testing tools go a step further by simulating real-world attacks. Ethical hackers attempt to exploit vulnerabilities under controlled conditions to assess how systems respond. The insights gained from these tests are invaluable for strengthening defenses before malicious actors can exploit weaknesses.

8. Access Control and Authentication Tools
Unauthorized access remains one of the leading causes of security breaches. Strong authentication mechanisms dramatically reduce this risk. Essential tools include:
- Multi-Factor Authentication (MFA)
- Single Sign-On (SSO) with secure identity providers
- Password managers
- Role-based access control (RBAC)
MFA, in particular, adds an extra layer of verification beyond passwords, making credential theft significantly less damaging. Limiting administrative privileges and regularly reviewing user permissions further minimizes exposure.
9. Backup and Disaster Recovery Tools
No security strategy is complete without a reliable backup system. Even the most robust defenses cannot guarantee absolute protection. Hardware failures, ransomware attacks, or insider threats can compromise systems unexpectedly.
Comprehensive backup tools should:
- Perform automated, incremental backups
- Store copies in secure offsite locations
- Allow rapid restoration
- Encrypt backup data
Effective disaster recovery planning ensures business continuity and reduces downtime. Regularly testing restoration procedures is equally important to ensure backups are usable when needed.
10. Continuous Monitoring and Security Audits
Website security is not a one-time setup—it is an ongoing process. Continuous monitoring tools provide real-time insights into system health, traffic anomalies, and suspicious behavior. Security audits, conducted periodically, evaluate policies, configurations, and compliance requirements.
Organizations should adopt:
- 24/7 monitoring solutions
- Automated security alerts
- Scheduled patch management
- Routine configuration reviews
Timely patching remains one of the simplest yet most effective defenses. Many successful attacks exploit known vulnerabilities for which patches already exist. Delayed updates create unnecessary risk.
Building a Layered Security Strategy
No single tool can provide complete protection against modern cyber threats. A resilient website security framework is built on a layered defense strategy, often referred to as “defense in depth.” Each layer addresses specific types of risks, collectively forming a robust shield around digital assets.
An effective layered approach typically includes:
- Firewall protection
- Encryption
- Malware monitoring
- Access control systems
- Regular vulnerability assessments
- Backup and recovery plans
Additionally, human oversight plays a vital role. Security awareness training, clear internal policies, and defined incident response procedures ensure that technology is supported by organizational discipline.
Conclusion
Website security tools are not merely technical add-ons—they are essential safeguards for digital operations. As cyber threats grow more sophisticated and relentless, organizations must adopt comprehensive, proactive security strategies supported by reliable tools and continuous vigilance.
By combining firewalls, encryption, malware detection, intrusion monitoring, vulnerability management, and strong authentication systems, businesses can significantly reduce their exposure to risk. Investing in security tools is not just a defensive measure; it is a commitment to protecting customers, preserving trust, and ensuring long-term operational stability in an increasingly hostile digital landscape.