As organizations continue to embrace containerization, distributing container images efficiently and securely has become a mission-critical requirement. Whether supporting microservices architectures, hybrid cloud deployments, or large-scale CI/CD pipelines, reliable container registry apps are foundational to modern software delivery. These tools do far more than store images—they enable version control, enforce security policies, optimize performance, and integrate seamlessly with development workflows.
TLDR: Container registry apps are essential for distributing container images securely and efficiently across development and production environments. They provide centralized storage, version control, access management, vulnerability scanning, and integration with CI/CD pipelines. Leading registries support automation, global replication, and compliance features that simplify modern DevOps workflows. Choosing the right registry depends on scalability needs, deployment models, and security requirements.
In this article, we examine how container registry applications streamline image distribution, explore key features to prioritize, and review respected platforms used by organizations worldwide.
Why Container Registries Matter
Containers package applications with all their dependencies, ensuring consistent performance across environments. But without a centralized and organized way to store and distribute these containers, teams face fragmentation, version drift, and security exposure.
A robust container registry app solves these problems by offering:
- Centralized image storage
- Version tagging and rollback capabilities
- Access control and authentication
- Vulnerability scanning and policy enforcement
- Global replication and caching
At scale, these capabilities ensure development teams can ship software quickly while operations teams maintain governance and visibility.
Core Features of Modern Container Registry Apps
Not all registries are built equally. Enterprise-grade solutions combine performance, compliance, and automation capabilities that go far beyond basic image hosting.
1. Secure Access Control
Security is a top concern when distributing container images. Registries typically provide:
- Role-Based Access Control (RBAC)
- Integration with identity providers (LDAP, SSO, OAuth)
- Signed image verification
- Private and public repository segmentation
This ensures only authorized users and systems can push or pull images, reducing the risk of tampering or data leakage.
2. Vulnerability Scanning and Compliance
Modern registry apps frequently integrate automated image scanning tools to identify known vulnerabilities in dependencies. Security scanning typically includes:
- Operating system package analysis
- CVE detection
- License compliance checks
- Policy-based image blocking
This proactive approach to security allows organizations to block compromised images before they reach production.
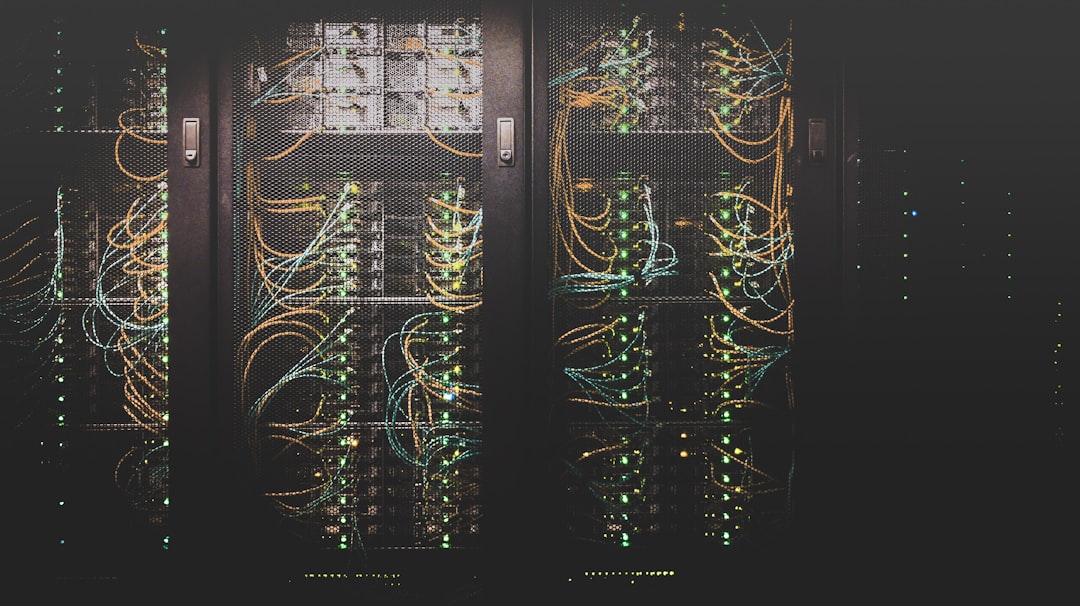
3. High Availability and Global Replication
For distributed teams and global deployments, proximity matters. Leading container registries support:
- Multi-region replication
- Edge caching for faster pulls
- Load-balanced architecture
- Failover redundancy
This minimizes latency and ensures application deployments remain resilient.
4. CI/CD Pipeline Integration
Modern development workflows rely heavily on automation. Registry apps seamlessly integrate with CI/CD systems to enable:
- Automated image builds and pushes
- Tagging based on commit or release versions
- Immutable artifact storage
- Rollback management
By embedding registry interactions directly into pipelines, teams eliminate manual steps and reduce human error.
Types of Container Registry Solutions
Organizations can choose between several deployment models depending on infrastructure and governance needs.
Public Cloud Registries
Major cloud providers offer managed container registry services. These platforms typically provide seamless integration with cloud-native services such as container orchestration, IAM systems, and monitoring tools.
Advantages include:
- Fully managed infrastructure
- Elastic scalability
- Native cloud integration
- Reduced operational overhead
Self-Hosted Registries
For organizations with strict compliance or data sovereignty requirements, self-hosted registries provide complete control over infrastructure and access policies.
Benefits often include:
- On-premise deployment
- Air-gapped environment support
- Custom security configurations
- Greater regulatory alignment
Hybrid Registry Architectures
Many enterprises adopt hybrid approaches, synchronizing on-premise and cloud registries through replication features. This model balances performance, compliance, and scalability.

Leading Container Registry Applications
Several container registry applications have emerged as trusted solutions across industries. While capabilities vary, the following platforms are widely respected:
Docker Hub
As one of the most recognized public registries, Docker Hub offers both public and private repositories. It is particularly popular among startups and open-source communities due to its vast ecosystem and accessibility.
Harbor
Harbor is an open-source registry that emphasizes security and compliance. It includes vulnerability scanning, content signing, RBAC, and replication policies. Its flexibility makes it suitable for enterprise deployment.
Amazon Elastic Container Registry (ECR)
Designed for integration with AWS services, ECR provides scalable image storage and automated lifecycle policies. Its native integration with AWS IAM strengthens access governance.
Google Artifact Registry
Google’s solution extends beyond container images to support multiple artifact formats. It integrates closely with Google Kubernetes Engine and other cloud services.
Azure Container Registry
Microsoft’s registry solution integrates into Azure DevOps pipelines and Active Directory, offering enterprise-grade security and geo-replication capabilities.
Operational Best Practices for Efficient Image Distribution
Even with advanced registry software, organizations must implement sound operational practices to maximize efficiency.
Use Immutable Tags
Avoid overwriting existing tags. Immutable tagging prevents inconsistencies and ensures reliable rollbacks.
Implement Image Lifecycle Policies
Automated cleanup policies help remove unused images, reduce storage costs, and maintain registry performance.
Scan Images Early
Shift security scanning earlier in the development lifecycle to detect vulnerabilities before images are pushed.
Enable Content Trust and Signing
Digitally signed images verify authenticity and help prevent supply chain attacks.
Monitor Registry Metrics
Track pull frequency, storage usage, and replication performance to support scalability planning.

Security Considerations in Container Image Distribution
The rise of software supply chain attacks has elevated registry security to a board-level concern. Container registries often represent a central distribution point, making them attractive targets for malicious actors.
Organizations should implement:
- Multi-factor authentication (MFA)
- Network segmentation and firewall controls
- Encrypted data at rest and in transit
- Continuous vulnerability intelligence updates
In high-security environments, air-gapped registry deployments ensure no external connectivity, further mitigating exposure risks.
Evaluating the Right Registry for Your Organization
Choosing a container registry app requires careful analysis of operational requirements and long-term scalability goals.
Key evaluation criteria include:
- Projected storage growth
- Geographic distribution of deployment environments
- Compliance obligations
- Integration with existing CI/CD tools
- Security and governance requirements
Enterprises often favor solutions that minimize friction with existing infrastructure while enabling automation and security at scale.
The Future of Container Registries
The ecosystem surrounding container distribution continues to evolve. Emerging innovations include:
- Artifact registries supporting multiple formats
- Enhanced supply chain security frameworks
- AI-driven vulnerability detection
- Integrated policy-as-code enforcement
As Kubernetes and cloud-native architectures grow in sophistication, registries will increasingly serve as secure artifact hubs rather than simple storage repositories.
Conclusion
Container registry apps are indispensable components of modern software delivery infrastructure. They enable secure, scalable, and automated distribution of container images across increasingly complex environments. By offering advanced security controls, high availability architectures, and seamless CI/CD integration, today’s leading registries empower organizations to innovate rapidly without sacrificing governance.
Selecting the right registry is not simply a technical choice—it is a strategic decision that affects operational resilience, compliance posture, and long-term scalability. Organizations that invest thoughtfully in container image distribution infrastructure position themselves for sustainable, secure growth in an increasingly container-driven world.